We Define IT Consulting
The IoT, or Internet of Things, is everywhere. There’s a relatively good chance that a device that would be part of the IoT is within your reach right now, perhaps even on your person. Businesses of all kinds use the IoT for various purposes as well, but behind this usage lies significant risk from cyberthreats, and a shocking number of businesses seem to accept this risk without much concern… as in, the vast majority of surveyed businesses utilizing the IoT demonstrated a lack of protection, but seemed not to be bothered by it.
One major nonprofit has become the victim of a disclosed major data breach, affecting 890 schools all across the US: the National Student Clearinghouse, or NSC. The organization has announced that they have experienced a considerable data breach that has put their clients’ data at risk. What does this mean for affected organizations and their clientele?
These days, data privacy is absolutely critical in both a business and individual context. In some locations, governments have introduced legislation to protect consumers, and in others, there is significant pushback in favor of fewer regulations on business. How does data privacy factor into your business’ operations?
You might see encryption as a major benefit to your cybersecurity strategy, but it’s often used in a way that might have you guessing whether you really understand it. Let’s take a closer look into what encryption does to your data, as well as why it is essential for any business to ensure maximum privacy and security.
How often does your company take it upon itself to ensure that those working for its success—your employees—are kept up to speed on cybersecurity? If your approach is to have your team sit in a room and watch a presentation once a year, it’s time to reconsider your training strategy. Let’s talk about the impact that proper cybersecurity training can have, and who tends to have access to it.
We discuss phishing often on this blog, and one method that often flies under the radar is smishing, or phishing that is conducted through SMS messages. Although email phishing is perhaps the most common method of conducting these scams, you should also be prepared to take on smishing, as it comes with its own share of unique challenges and dangers.
Scams are everywhere in our highly digitized world, which makes it especially important that everyone is prepared to deal with them—both personally and professionally. The publication Consumer Reports’ cover feature for its August 2023 edition is dedicated to exactly this goal: helping its readers avoid the various scams and threats out there. Let’s look at some of the advice shared in the article, and compare it to the best practices we recommend.
In 2004, a service called VirusTotal was launched and swiftly became a popular antivirus and malware scanner to help detect threats in various files and URLs. It became popular enough that it was officially acquired by Google in 2012 and ultimately assimilated into Chronicle, a cloud-based security operations suite for enterprise businesses. Despite this impressive pedigree, however, we find ourselves able to look to VirusTotal as a sobering reminder of how fickle cybersecurity can be, with the service being the source of some limited data exposure.
Amazon Prime subscribers recently received an email from the online marketplace, warning them of the prevalence of scams that took advantage of their offerings and brand recognition. Let’s go through the advice that this email shared, and compare it to the best practices we recommend for avoiding scams.
Nowadays, you can’t afford not to have some portion of your business’ budget set aside for cybersecurity. The question is, how much do you need, and what should you be spending it on first? Let’s take a few moments to dig a little deeper into this question and examine a few cybersecurity protections you should establish as your business’ baseline defenses.
The IoT—the Internet of Things—is a fascinating technology, as it exemplifies just how much can be accomplished when Internet connectivity is used to augment the capabilities of otherwise “dumb” devices. Unfortunately, as fascinating as it is, the IoT is also infamous for its security issues…a reputation that attackers have been perpetuating as these devices grow more common.
AI—artificial intelligence—has been a hot topic as of late, with it seemingly being used for any purpose you can imagine nowadays. Unfortunately, this has also included cybercrime.
However, just as AI can be a weapon for cybercriminals to use, it can also be a shield to help protect your business from threats. For instance, in phishing prevention.
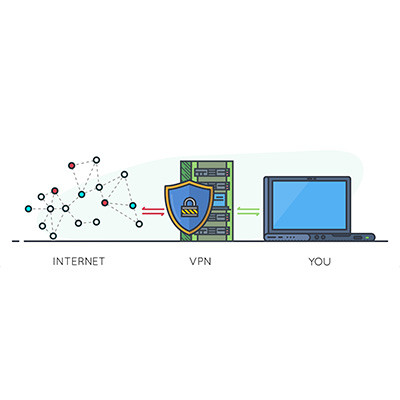
When it comes to security, one often overlooked tool is the virtual private network, or VPN. We recommend that all businesses use a VPN to keep remote and hybrid workers from inadvertently putting your business’ data at risk while out of the office. Let’s go over why a VPN is so effective, as well as what you should look for in a business-grade VPN tool.
Businesses cannot afford to grow complacent with their network security, as it could make a significant difference between falling prey to an attack and remaining secure. The process of securing a network must be looked at holistically, from top to bottom. This idea of enterprise security is not new, but even a small business needs to keep it in mind, and these solutions are more accessible than you might think.