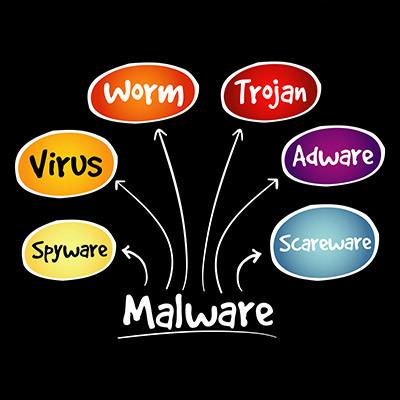
Network security could mean any number of things, but more often than not, people are using the term as a blanket statement against the dreaded idea of malware and its many forms. Today, we are discussing how vast the world of malware can be and how often you might find yourself misunderstanding what it exactly is. Knowing all this can help you identify if you have become a malware victim or not.
We Define IT Consulting
Microsoft has planned an increase in the price of its software offerings Microsoft 365 and Office 365, and make no mistake, it will impact your business in some way whether you are ready or not. We are writing this blog to share information that you might find important about this price increase so you can plan to get the most out of your software moving forward.
If you have tried to procure hardware or products over the past couple years, chances are you have noticed that it is harder to find them than usual. This is particularly the case for any companies that have dealings with computing hardware, as the price has been hiked considerably on even the most basic of components. What has triggered this dramatic change in the technology supply chain, and what can be done about it?
It’s not often that something profoundly changes the landscape of business technology management as much as managed services has. When implemented correctly, managed IT services can completely replace the traditional methods of technology management within a company, and it all starts with changing not just your budgeting practices but also your maintenance practices.
More workplaces than ever before are utilizing the power of remote technology, but this also creates problems with security that must be addressed. How can you ensure that your organization isn’t putting itself at risk as a result of this general displacement of your workforce? Let’s discuss some action items you might choose to implement for your business.
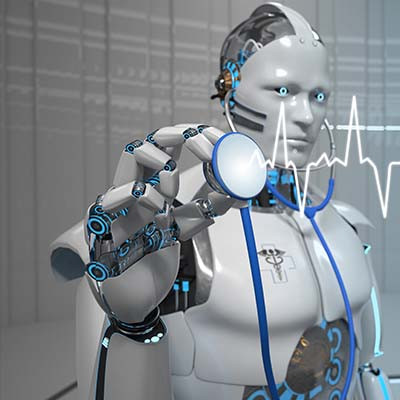
Healthcare is an industry that—quite understandably—operates under very high pressure for a significant share of the time. As a result, it is only natural to conclude that a technology that could potentially make the lives of healthcare providers and administrators easier in numerous ways shows some promise. That technology is artificial intelligence.
Let’s go over a few of the many ways that AI has been proposed (if not implemented already) as a solution to some of healthcare’s more challenging stresses.
When we talk about data privacy in a business, the default is to generally think about the data the business has collected and compiled from its clientele. However, that’s just one type of data a business has. There’s also a lot of data that is collected by the business about that business’ employees. So, how well protected is this data?
The cloud is one way that businesses are changing their operations for the better. Not only does the cloud enable organizations to function in drastically different ways from the status quo, it also gives businesses countless opportunities to reduce costs. Here are just a few ways you can expect the cloud to reduce your expenses and improve your return on investment for IT resources.
Look, we are big fans of the cloud, especially for data storage, but you shouldn’t implement the cloud without a solid security strategy. Whether you are using it for your business’ data storage needs or just to take backups of your infrastructure, you’ll still need to keep various facets of security in mind for your cloud storage. It all starts with figuring out how secure your cloud provider really is.
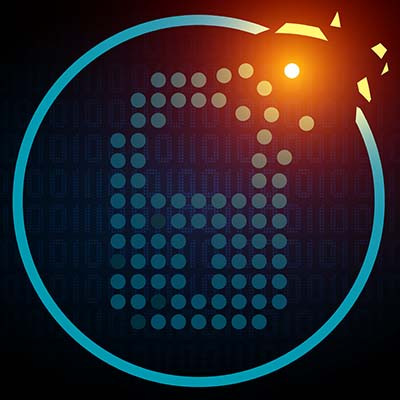
Cybersecurity is an important subject for a business’ entire team to appreciate, particularly when it comes to the minute differences between different terms. For instance, a layperson might hear “breach” and automatically think “security incident.” While this technically isn’t incorrect, per se, the two terms aren’t really synonymous.
Let’s take a few moments to dive into the minutiae and define these two terms more clearly.
While remote work has been a relatively new option for many businesses currently using it in their operations, it has already shown considerable benefits. Having said that, it would be incongruous of us if we didn’t also acknowledge one glaring issue that remote work has helped to foster: a sense of disconnect in many of those making use of it.
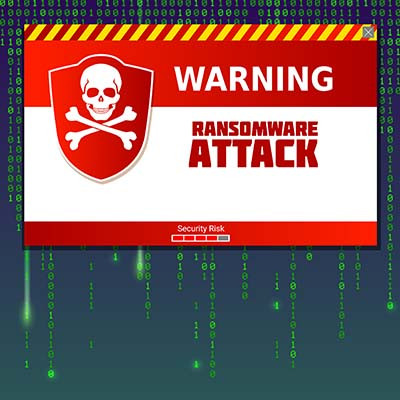
Ransomware is widely regarded as one of the worst modern cyberthreats out there today, and there's plenty of evidence to support this. These attacks and their aftereffects can devastate businesses of all industries. Let's consider why it is that ransomware is so dangerous, and what can be done to fight it.
Smart devices are everywhere, with the Internet of Things (the blanket term for any device that connects to the Internet for added functionality) growing larger each day. While this is great for convenience (and in many cases, the "cool factor") it can have some chilling ramifications for cybersecurity.
Cloud computing has been a hot topic in IT circles for a few years. First because of the skepticism that many IT professionals had for the practice, and now that it is a mainstream business technology, ways to boost security to protect the organization who has embraced this computing strategy. We’re here to tell you that while cloud computing is convenient, flexible, and seemingly affordable, there are instances where having physical machines makes more sense for a business.
There are times when you experience computer problems and you might hesitate to call in the big guns to resolve the issue. Unfortunately, the reality is that many businesses are under the impression that calling experts to handle their computer problems will leave them in a difficult position financially. We’re here to make sure that doesn’t happen! Here are three common computer repair problems that you might—just might—be able to solve in a simple and easy way.
When it comes to your desktop infrastructure, your company has several different options available to it, one of which is Desktop-as-a-Service. How does this option compare to having a traditional workstation, and why might a small business get value out of Desktop-as-a-Service? Let’s take a closer look at what DaaS involves.