We Define IT Consulting
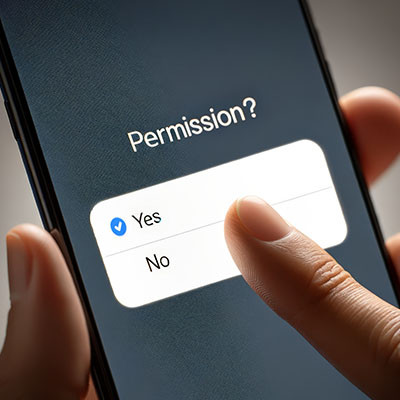
At the beginning of this year, a massive data breach struck a location data broker called Gravy Analytics and took possession of a dataset with 30 million points from devices worldwide. This data could potentially be used to track individuals and their movements, tellingly, through healthcare, government, and military facilities.
Unfortunately, nothing can be done about data that has already been breached, but preventative steps can and should be taken to protect your business. Let’s discuss how to prevent your applications from tracking your movements.
If you want more productivity from the workday, then multiple monitors can help you achieve this goal. You might run into the issue of “ghost monitors,” though, where your PC believes you are connected to screens when you’re not. If you experience this issue and your application windows are off-screen and unobtainable, you’ll find this week’s tip helpful.
Your Android device offers a lot of capabilities in its little frame, with many people relying on theirs to keep their lives organized and generally handled. Many businesses even rely on Android mobile devices. This should only reinforce how critical privacy and security are.
In light of this, we’ve shared a few simple tips anyone can do to help make a smartphone that much more secure.
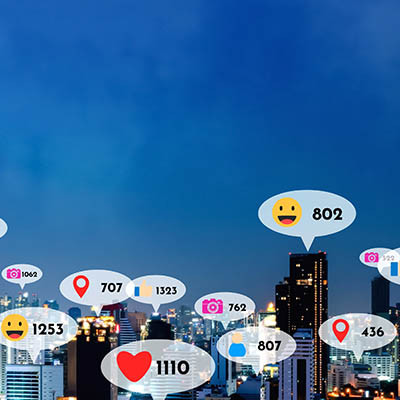
Bluesky is the new kid in town regarding social media platforms, which means that most users may not have a significant following on it yet… and new users may not be following many at all. However, a few baked-in options make it much simpler for the latter to curate their experience on the platform.
Let’s go over how a user can find new accounts to follow on Bluesky.
Sometimes problem solving requires you to step away and think about the issue at hand. Consider any great strategist out there and you’ll understand that it takes time and calculation to make moves that will benefit you now and in the future. Today, we’ll explore how you can be more productive through strategic pausing.
X The Everything App®, formerly Twitter, has been experiencing a massive user loss for the past few weeks, with everyone from celebrities to average people evacuating from the platform. If you wish to join them for any reason, we’re sharing the process for fully extricating yourself and your data from this specific social media network.
Modern wisdom states that if you’re not paying for a product, you’re the product.
For all the good the Internet is capable of doing, it is equally capable of being extremely harmful… especially when data is involved. Websites and social media platforms collect data from their users and track their movements across the Internet, sell it to advertisers, and more recently, use it to train AI.
Let’s go over what you can—and arguably should—do to limit these platforms' ability to do so.
Windows 11 takes a page out of Apple’s design playbook and features a taskbar that, instead of being off to the side, is smack in the middle of the toolbar. While some may like this change, others may not.
Fortunately for these others, a simple setting change can return the taskbar to its familiar place like on older versions of Windows.
Windows 11 features a robust desktop environment with a lot of neat tricks and customizations to work more effectively. Controlling your Windows desktop experience can enhance productivity and streamline the way you interact with your computer. In today’s blog, we give you four tips to help you customize and manage your Windows environment more efficiently.
Artificial intelligence is everywhere, and it is making data more valuable than ever. This is because AI platforms rely heavily on data to function effectively. Many platforms and services collect data from their users to fuel these algorithms. LinkedIn has recently been found to do this—by default—without properly informing its users or updating its terms of service.
If you are a Gmail user, you might have noticed the different inbox categories available. This makes it much easier to reach “inbox zero.” With the “priority inbox,” you can achieve this feat without so much as breaking a sweat—unless you count sweat from how much you’re laughing at how easy this tip is to pull off.
You can do everything in your power to secure your social media accounts and lock down your privacy settings. Still, at the end of the day, social media users expose themselves to a torrent of information and content every time they log on. As a civilization, we’ve never really had something like this before. These platforms curate content that the user wants to see to keep the user coming back and staying longer. It’s inherently designed to be enticing and addicting, which is dangerous for certain individuals.
Then, there are scams and an endless stream of grifts that pose a wide range of additional problems for users.
Let’s talk about ways you and those you care about can be safer on social media.
Social media is constantly evolving, and if the big social networks had it their way, it would be the only place people go when they log onto the Internet. Whether you have strong feelings for or against social media, or perhaps you are indifferent, it’s important to understand how to protect yourself when using social media.
Have you ever seen the file types that look like normal folders, but they have a zipper on the icon? These are ZIP files, and they are helpful for a variety of reasons. We’re sure you have encountered zipped files throughout your time using technology, and today, we want to demystify them a little bit and show you how to use them effectively.
While AI is far from perfect, I always love discovering ways that it can help do something mundane and speed up a workflow here or there. I’m no expert in Photoshop either, so if I need to edit something, I usually depend on someone with a little more experience, but this was a really neat trick I was able to do in just a few minutes!
Note taking apps are really useful and Microsoft OneNote is one of the most available and feature rich apps on the market for this use. You are probably familiar with the sticky note. They are notes that give a solid visual representation of items that workers need to be cognizant of for all types of processes. In today’s blog, we will go through the process of creating “sticky notes” in OneNote.
There will always be times when you have to invite guests and other external users to your Microsoft Teams meetings, especially if you want to take advantage of the many collaboration options offered through the platform. However, you need to be very careful with guests and external users–especially in today’s cybersecurity-centric world.